Help
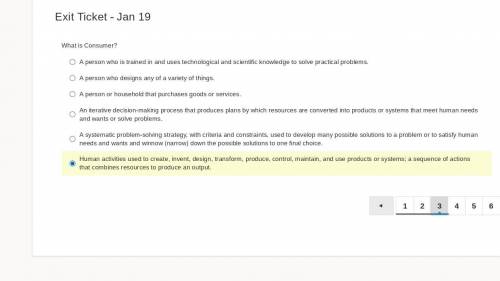
i accidently chose the last one
...

Answers: 3


Another question on Computers and Technology

Computers and Technology, 22.06.2019 22:40
Write a program that defines symbolic names for several string literals (chars between quotes). * use each symbolic name in a variable definition. * use of symbolic to compose the assembly code instruction set can perform vara = (vara - varb) + (varc - vard); ensure that variable is in unsigned integer data type. * you should also further enhance your symbolic logic block to to perform expression by introducing addition substitution rule. vara = (vara+varb) - (varc+vard). required: debug the disassembly code and note down the address and memory information.
Answers: 3

Computers and Technology, 23.06.2019 07:00
You need a quick answer from a coworker. the most effective way to reach your coworker is through a. cloud server b. instant message c. teleconference d. telepresence
Answers: 1

Computers and Technology, 25.06.2019 01:00
What phrase indicates someone has knowledge and understanding of computer,internet,mobile devices and related technologies?
Answers: 1

Computers and Technology, 25.06.2019 10:00
Which of the following methods could be considered a “best practice” in terms of informing respondents how their answers to an on-line survey about personal information will be protected? the investigator uses the informed consent process to explain how respondent data will be transmitted from the website to his encrypted database without ever recording respondents’ ip addresses, but explains that on the internet confidentiality cannot be absolutely guaranteed. respondents are informed that investigators will try to keep their participation confidential; however, confidentiality cannot be assured. the investigator uses the informed consent process to explain her institution’s method for guaranteeing absolute confidentiality of research data. respondents are informed that a research assistant will transfer all the research data to a password-protected computer that is not connected to the internet, via a usb flashdrive. the computer is located in a research team member’s office.
Answers: 2
You know the right answer?
Questions


Mathematics, 10.02.2020 19:39

English, 10.02.2020 19:39



English, 10.02.2020 19:39

Mathematics, 10.02.2020 19:39



Biology, 10.02.2020 19:39

English, 10.02.2020 19:39


Mathematics, 10.02.2020 19:39


Mathematics, 10.02.2020 19:39

English, 10.02.2020 19:39