Computers and Technology, 25.09.2020 02:01 chayaharroch03
Compute and print an order from Taco Bell.
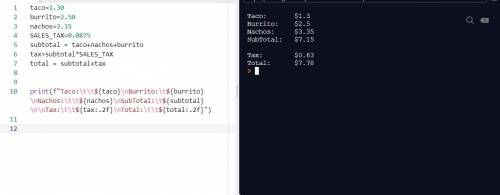
a) Create a variable taco and assign it the value 1.30
b) Create a variable burrito and assign it the value 2.50
c) Create a variable nachos and assign it the value 3.35
d) Create a constant variable SALES TAX and assign it the value .0875
e) Calculate the subtotal of an order containing a taco, burrito and nachos.
f) Calculate the tax of that same order.
g) Calculate the total of that order including tax.
h) Use f-string formatting, newline and tabs to precisely match the output
Output Example ORDER:
Taco:
Burrito:
Nachos:
SubTotal:
$1.30
$2.50
$3.35
$7.15
Tax:
Total:
$0.63
$7.78

Answers: 3


Another question on Computers and Technology

Computers and Technology, 23.06.2019 13:10
What is domain name system (dns)? allows dynamic ip address allocation so users do not have to have a preconfigured ip address to use the network converts ip addresses into domains, or identifying labels that use a variety of recognizable naming conventions the efficient coexistence of telephone, video, and data communication within a single network, offering convenience and flexibility not possible with separate infrastructures the integration of communication channels into a single service
Answers: 2

Computers and Technology, 24.06.2019 02:00
Which steps will open the system so that you can enter a question and do a search for
Answers: 1

Computers and Technology, 24.06.2019 16:30
What is the item which could be matched with a statement below? software installed on a computer that produces pop-up ads using your browser an example of social engineering malware loads itself before the os boot is complete type of spyware that tracks your keystrokes, including passwords windows key + l the practice of tricking people into giving out private information or allowing unsafe programs into the network or computer when someone who is unauthorized follows the employee through a secured entrance to a room or building a type of malware that tricks you into opening it by substituting itself for a legitimate program a computer that has been hacked, and the hacker is using the computer to run repetitive software in the background without the user's knowledge an infestation designed to copy itself repeatedly to memory, on drive space, or on a network
Answers: 1

Computers and Technology, 24.06.2019 17:40
Write a program that begins by reading in a series of positive integers on a single line of input and then computes and prints the product of those integers. integers are accepted and multiplied until the user enters an integer less than 1. this final number is not part of the product. then, the program prints the product. if the first entered number is negative or 0, the program must print “bad input.” and terminate immediately
Answers: 2
You know the right answer?
Compute and print an order from Taco Bell.
a) Create a variable taco and assign it the value 1.30 <...
Questions

Advanced Placement (AP), 22.06.2019 10:40

Biology, 22.06.2019 10:40

Chemistry, 22.06.2019 10:40



English, 22.06.2019 10:40


History, 22.06.2019 10:40


Social Studies, 22.06.2019 10:40




Biology, 22.06.2019 10:40



Biology, 22.06.2019 10:40

Computers and Technology, 22.06.2019 10:40