Computers and Technology, 30.03.2020 21:59 july00
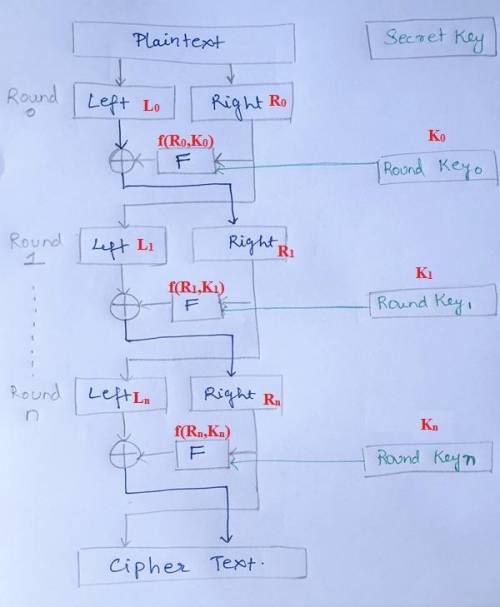
A. The DES algorithm is based on the idea of the Feistel cipher. Explain how the Feistel cipher structure achieves substitution and permutation. b. A secure block cipher must be able to achieve strong confusion and diffusion in order to be able to viably resist cryptoanalysis. Explain what these concepts mean and why they are important.

Answers: 1


Another question on Computers and Technology

Computers and Technology, 22.06.2019 11:20
The kurt vonnegut commencement speech, the neiman-marcus chocolate chip cookie recipe, and the get-well emails to the dying boy are examples of select one: a. social engineering b. hoax emails c. email viruses d. worms
Answers: 1

Computers and Technology, 23.06.2019 06:30
When early motion pictures played in movie theaters, they were often accompanied by live organ or piano music. which of the following are the most likely reasons that this happened? (select all that apply). the music was provided to distract audience members from the loud sounds made when filmstrips were changed. the music accompanied the movies because the movies were silent and audiences were used to hearing music during plays in theaters. the music usually was played before, and sometimes after the movie, as an alternative form of entertainment. the music viewers to interpret the dramatic action in the films.
Answers: 2

Computers and Technology, 24.06.2019 13:00
In a heat transfer course, we can derive the equation for the temperature distribution in a flat rectangular plate. in this example, we will look at a plate at steadystate with three sides being held at t1, and one side held at t2. the temperature for any location on the plate, t(x,y), can be calculated by where create a function (prob3_5) that will take inputs of vectors x and y in feet, scalar n, scalars l and w in feet and scalars t1 and t2 in degrees fahrenheit. it will output a matrix t which is the temperature of each x and y locations. t will have the number of columns equal to the number of elements in x and rows equal to the number of elements in y. though this can be done without loops (perhaps more efficiently), your program must use a nested loop.
Answers: 2

Computers and Technology, 24.06.2019 13:30
To move an excel worksheet tab, simply right-click on it drag and drop it double-click on it delete it
Answers: 1
You know the right answer?
A. The DES algorithm is based on the idea of the Feistel cipher. Explain how the Feistel cipher stru...
Questions


English, 15.12.2020 23:10





Spanish, 15.12.2020 23:10



Mathematics, 15.12.2020 23:10

Advanced Placement (AP), 15.12.2020 23:10



Biology, 15.12.2020 23:10

English, 15.12.2020 23:10



Mathematics, 15.12.2020 23:10