(brainliest ! )
our agents have been intercepting messages between two hackers trying to...

Computers and Technology, 13.01.2020 18:31 brisamauro27
(brainliest ! )
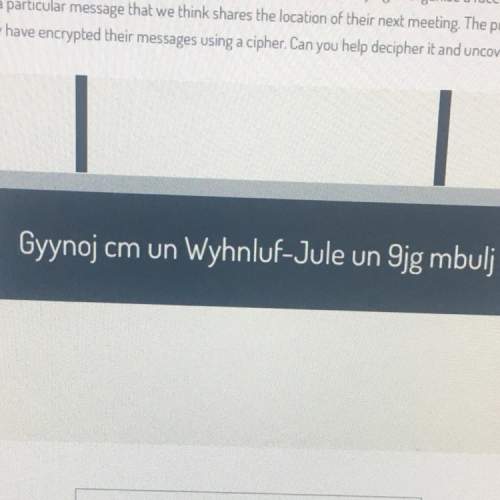
our agents have been intercepting messages between two hackers trying to organise a face-to-face. we've
identified a particular message that we think shares the location of their next meeting. the problem we have
is that they have encrypted their messages using a cipher. can you decipher it and uncover the location?

Answers: 1


Another question on Computers and Technology

Computers and Technology, 22.06.2019 23:00
Which factor is the most important when choosing a website host? whether customers will make secure transactions the number of email accounts provided the purpose of the website the quality of the host control panel
Answers: 3

Computers and Technology, 23.06.2019 04:31
Q14 what is most important for you to choose before you build a network? a. private network b. nos c. network media d. network protocol e. directory service
Answers: 1

Computers and Technology, 23.06.2019 07:10
If you want to import a picture into a dtp application, what must you do first? draw an image frame. import text. open the folder containing the file. select get image… from the windows menu.
Answers: 2

Computers and Technology, 23.06.2019 11:00
What are the possible consequences of computer hacking? what is computer piracy? describe some examples. what are the effects of computer piracy? what are the possible consequences of computer piracy? what is intentional virus setting? describe some examples. what are the effects of intentional virus setting? what are the possible consequences of intentional virus setting? what is invasion of privacy? describe some examples. what are the effects of invasion of privacy? what are the possible consequences of invasion of privacy? what is an acceptable use policy and what is the purpose of the acceptable use policy what is intellectual property and how can you use it?
Answers: 1
You know the right answer?
Questions


Mathematics, 11.01.2021 18:40


Mathematics, 11.01.2021 18:40



Mathematics, 11.01.2021 18:40


English, 11.01.2021 18:40


Mathematics, 11.01.2021 18:40


Mathematics, 11.01.2021 18:40


World Languages, 11.01.2021 18:40



Mathematics, 11.01.2021 18:40




